The idea that someone might have bugged your home or your office to learn information about you might sound pretty out there. It’s the sort of thing that you see in spy movies, or major thrillers, and the idea that this could actually happen in the real world is almost beyond belief.
And yet all you need to do is look at the example of Matt Hancock, the former Health Secretary who recently resigned/was sacked (depending on who you believe) after a camera in his office was moved and then footage was stolen, exposing his extra-marital affair with Gina Coladangelo in the national media.
While the camera in this instance was a normal CCTV one that already existed, the fact that it was moved and used in such a way shows that people aren’t safe from bugging. And it isn’t just major politicians that need to be concerned. Bugging rooms or technology is now an accessible method to spy on someone. If you have the right contacts then you could, in theory, try to steal business secrets or monitor your spouse if you think they are cheating.
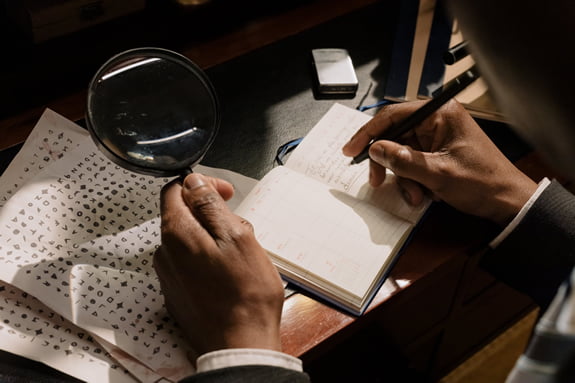
So what do you do if you’re concerned about being bugged? You turn to the experts. At EJM Investigations we have our own engineer who is specially trained in debugging. It’s not a job we leave to our private investigators as it requires specific, expert knowledge in this field. If you’re concerned that you think you might be being bugged, we can do a sweep and let you know.
Nine times out of ten you will probably find that there’s nothing there – but there’s nothing like the peace of mind of having it confirmed.
Debugging Locations
Here are some of the places that could be bugged, and why:
Home
Someone may film or record you at home, or try to track your online activities. Home bugging is often the result of a suspicious partner who wants to catch you cheating on them, or sometimes an ex-spouse looking for advantages ahead of divorce proceedings or even custody battles.
Office
Your office may be bugged with recording devices or software by a competitor looking to gain an edge over you, or a disgruntled employee who wants to expose your business for their own personal gain.
Factory
Similar to the office, your factory floor might be bugged by someone who wants to learn more about your processes or that is trying to discover evidence of healthy and safety violations to use against you, even if they are misrepresented.
Vehicle
Your car or van may be tracked by an overbearing employer, or by a spouse who wants to control you or know where you’re driving.
Electronic equipment
Anything electrical can be bugged in some way. Even the most unassuming of household or office objects, like an electronic clock or a light fitting, could contain a bug being used to record or monitor you.
Clothing
It’s possible for microdevices that record sound or track your location to be inserted into the lining of your clothing. This isn’t one to get paranoid about, because these are extremely high-tech devices that would only be used in the most serious of cases. They are very rare. Despite that, our expert is more than capable of locating them.
Bug Technology
There are three main types of bug that can be used – here’s what they are.
Camera
As Matt Hancock found out, a hidden camera can really cause you some headaches. Modern cameras are tiny but record footage in extremely high detail, meaning it’s surprisingly easy to capture clear video that could reveal business secrets, or even just record you in private moments that could then be used for illicit purposes such as blackmail.
Our expert is able to draw on their experience of camera tech to do a complete sweep of your room. They know exactly what to look for, and can disable any cameras if required, or at least let you know where they are ready for an investigation to continue.
Listening devices
Listening devices could include microphones to record general audio in a location, or more sophisticated tech that can record phone calls made to your landline or mobile. If you’re a business owner discussing sensitive information, a bug can cause major problems as competitors gain information they can use to scupper your deals.
Using our expert, we have technology that can detect audio recording and listening devices and remove them safely.
Tracker
Trackers in your vehicle work by either sending live information about your whereabouts to a remote server, or simply record the information on an internal memory card, ready to be collected and analysed at a later date.
We can identify trackers, and then either leave them running once we’ve informed you that you’re being watched, or remove them. Leaving them active while you gather evidence on who has bugged you is often the right course of action in the short term.
Computer Software
Someone may have managed to install software onto your PC or laptop to record you activities online. It’s similar to a virus, but could be used for reasons other than robbing you. We can find the software and block it.
Bring In The Experts
If the above has got you thinking, and you’re a little worried that someone might have bugged you to learn some information about you, or to gain leverage, then get in touch. We can help put you at ease, and if we do find anything then we’re also able to use our wide range of skills to try and track down the perpetrator, or at least to gather the essential evidence needed to hand your case over to the police.
One thing that’s really critical though – don’t contact us using any technology you think might be compromised, or from a room that you think is bugged. If you are being listened to, you’ll tip off the person bugging you and they could start to hide evidence, or they may try to intimidate you.
Instead, use someone else’s phone in a public location, and call 01772 334700.